A Comparative Analysis of Consequence-Driven OT Network Design
Against the Dragos 2026 OT Cybersecurity Report Findings
John E. Hargrove, P.E. (TX)
JohnEHargrovePE Consulting • Buna, Texas
February 2026
| ABSTRACTThe Dragos 2026 OT Cybersecurity Report identifies six structural conditions that allow nation-state threat actors — notably Volt Typhoon, tracked by Dragos as VOLTZITE — to maintain persistent, undetected access inside U.S. critical infrastructure. This paper examines those six conditions against a decade of engineering work spanning 2009 to 2019 across a network of rural electric cooperatives in East Texas. That program encompassed point-to-point microwave network expansion, AMI substation power metering at dozens of substations, generation assets totaling nearly 900 MW, and interties with multiple Investor-Owned Utility transmission networks serving the region — representing a total investment of approximately $12–15 million over ten years. The program served East Texas generation and transmission cooperatives and their distribution cooperative members across a geographically dispersed service territory, spanning the transmission grids of three regional IOUs. The central finding is that consequence-driven network design principles, applied at this scale and within the resource constraints of rural cooperative operations, directly addressed five of the six structural gaps described in the Dragos report in 2026. The purpose of this analysis is not to claim that this program solved a national problem. It is to demonstrate that the engineering logic which would have contained these threats was available, implementable, and documented — and that the organizations that remain most exposed today are exposed not because the solutions did not exist, but because the right questions were not being asked. |
I. Introduction
In February 2026, Dragos published its annual OT Cybersecurity Report. The report’s central conclusion was sobering but not surprising to those of us who have spent careers inside these systems: nation-state actors with pre-positioned access in U.S. critical infrastructure cannot be fully eradicated in the near term. The structural conditions that enable persistent, undetected adversary presence are embedded in how OT networks were built, how legacy systems are maintained, and how resources are distributed across thousands of operators with widely uneven security maturity.
The report also landed with me, with a specific kind of recognition. Every structural condition it describes — incomplete asset inventories, exposed industrial edge devices, fragile legacy systems resistant to conventional security controls, flat networks with no meaningful traffic baselines, and patient nation-state tradecraft designed to stay below detection thresholds — is a condition I worked against directly across a decade of engineering work in East Texas, beginning in 2009 across a network of rural generation, transmission, and distribution cooperatives in the region.
That work culminated in a paper presented at the 2019 IEEE Rural Electric Power Conference, describing a consequence-driven, cyber-informed network architecture built over a decade at a complex of rural generation and transmission cooperatives in East Texas. Reading the Dragos report against that documented engineering record produces a straightforward observation: the design principles applied from 2009 through 2019 directly address the structural vulnerabilities the Dragos report identifies as enabling national-scale adversary persistence in 2026.
This paper examines mapping in detail. The intent is not self-congratulation. The work described here had real limitations, which are acknowledged. The intent is to demonstrate that the engineering approach needed to address these threats is not exotic, was not unavailable in 2019, and remains applicable today for the class of organizations the Dragos report identifies as most at risk: smaller utilities, rural cooperatives, and municipal systems operating with limited staff and budget in the same threat space as the largest IOUs.
II. The Engineering Context: East Texas Cooperatives, 2009–2019
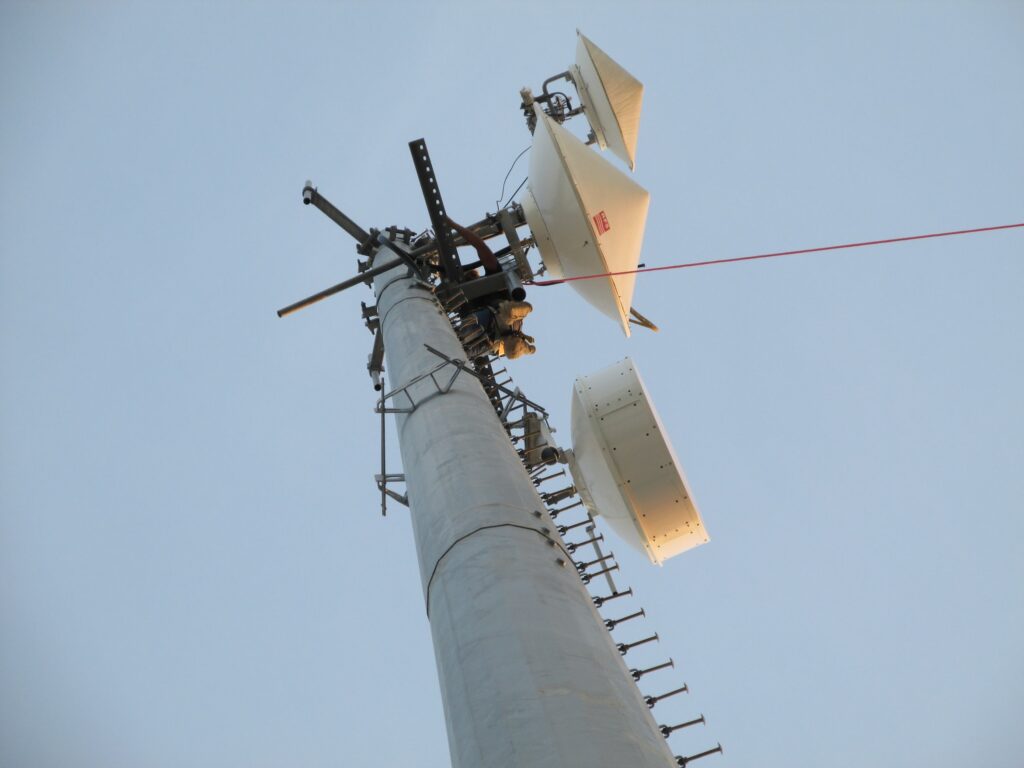
In 2009, I was engaged by a network of rural electric cooperatives in East Texas to begin what would become a decade-long infrastructure program. The initial scope involved expanding point-to-point microwave backhaul networks, establishing telemetry infrastructure for AMI substation power metering, and deploying Schneider 8650 ION meters at dozens of substations distributed across a large geographic area that spans the transmission territories of three regional Investor-Owned Utilities. The generation assets served by this network included three gas peaking units totaling approximately 700 MW, two hydroelectric units of 50 MW each, and one biomass unit of 90 MW — a diverse portfolio of generation types with correspondingly different telemetry, protection, and communications requirements. By the end of the program in 2019, total investment across the cooperatives had reached approximately $12 to $15 million, engaging dozens of cooperative staff, contractors, and vendors throughout.
The program was not managed as a formal multi-year project in the conventional sense. It was driven by a longer-horizon engineering vision — an informal but deliberate architecture for cyber-informed engineering and resilience that evolved as the network grew, the threat environment changed, and the cooperatives’ operational requirements deepened. This loose orchestration across multiple organizations over a decade is itself part of the case study’s relevance: it reflects how infrastructure decisions actually get made in the rural cooperative environment, where no single program manager controls the full timeline, budget, or organizational calendar. The security work described in this paper covers the full arc of that engagement, with the consequence-driven security architecture becoming progressively explicit from 2014 through 2019 as the network grew more complex and NERC CIP obligations came into effect.
The formal security architecture work proceeded in two recognized phases. Phase 1 (2014–2016) built on the existing microwave and IP/TDM backbone, establishing a resilient IP network with N-1 failure tolerance, migrating from flat Layer 2 to Layer 3 OSPF routing, and placing internal firewalls at major isolation boundaries. This phase was focused primarily on operational reliability, with NERC CIP compliance as a concurrent obligation. Phase 2 (2016–2019) was triggered by an honest engineering reassessment. When the reliable IP network was expanded in 2016 to serve additional member cooperatives, it became clear that the attack surface had grown in ways not fully anticipated. The response was a fundamental architectural shift: displacing OSPF with MPLS as the primary routing fabric; deploying UTM (Unified Threat Management) firewall systems specifically designed for ICS/SCADA environments at all segmentation boundaries; establishing per-substation isolation zones; implementing OS hardening per CIS Top 20 controls; deploying multi-factor authentication and 802.1X network access control; and building a centralized NOC/SOC with 24/7 coverage integrating a SIEM fed by firewall logs, router SYSLOG, SCADA server event logs, and Active Directory telemetry.

The design philosophy throughout was what Idaho National Laboratory would later formalize as Cyber-Informed Engineering: ask what physical consequence a cyber pathway could cause, and design that pathway out. The architecture was built around consequence, not compliance.
| Core Design PremiseOT cybersecurity is not about preventing every intrusion. It is about ensuring that the consequences of any intrusion are bounded, observable, and recoverable. This premise drove every architectural decision in this program. |
III. The Dragos 2026 Threat Landscape: Six Structural Gaps
The Dragos 2026 OT Cybersecurity Report identifies six structural conditions that collectively make complete adversary eradication technically and operationally infeasible in the near term. These are not technology failures or policy failures in isolation. They are embedded in the architecture and operational reality of U.S. critical infrastructure systems.
The six conditions, as described in the report, are:
- Structural visibility gaps in OT environments, including incomplete asset inventories and limited protocol-level monitoring
- Overexposed industrial edge devices and weak segmentation, creating direct OT network access via internet-facing gateways
- Legacy systems and safety constraints that prevent conventional patching, scanning, and agent-based security controls
- Low-noise adversary tradecraft using valid accounts and native tools that blend with normal administrative activity
- Scale, fragmentation, and uneven security maturity across thousands of public and private operators
- Absence of historical telemetry makes retrospective reconstruction of past intrusions impossible in many environments
The sections that follow examine each gap in turn, describing what the East Texas cooperative program did or did not do to address it, and what that means for operators working under similar constraints today.
IV. Gap-by-Gap Analysis
Gap 1: Structural Visibility Gaps in OT
What the Dragos Report Describes
OT environments often have incomplete asset inventories, limited logging, and minimal deep protocol monitoring — especially on legacy PLCs, RTUs, and serial-to-IP bridges. Defenders lack the telemetry to distinguish normal control traffic from adversary reconnaissance and persistence. Dragos attributes extended adversary dwell times not to exotic zero-days but to this fundamental visibility deficit.
What the Program Did
The 2019 program built a centralized SIEM fed by multiple sources: firewall logs from all zone boundaries, SYSLOG output from all network routers, event logs from SCADA servers, and Active Directory tracking of all device and user access events. The explicit goal was to establish per-zone traffic baselines to identify anomalies.
A critical design decision was to treat security monitoring as a subset of operational monitoring rather than a separate discipline. Because the same monitoring infrastructure that supported NOC operations also fed the SOC, the investment could be justified on operational reliability grounds before the security case was fully developed internally. This dual-use approach is essential for resource-constrained operators who cannot justify standalone security monitoring programs.
The program also directly addressed the asset inventory problem. The discovery process of building the SIEM baseline revealed devices and connectivity paths that were not in any formal inventory — exactly the condition the Dragos report identifies as endemic. These were not found through an administrative audit. They were found by instrumenting the network and observing which devices were actually talking to which.
| Lesson for OperatorsYou cannot baseline what you cannot see, and you cannot detect anomalies without a baseline. Start by instrumenting zone boundaries — even basic firewall logging with SYSLOG aggregation gives you the traffic observation point from which a real baseline can be built. The monitoring process itself will complete your asset inventory. |
Gap 2: Overexposed Industrial Edge and Weak Segmentation
What the Dragos Report Describes
Volt Typhoon (VOLTZITE) has focused heavily on compromising Sierra Wireless AirLink and similar cellular gateway devices that bridge directly into OT networks, bypassing traditional perimeter controls. These devices were added for operational convenience — reducing truck rolls, improving remote SCADA polling reliability — but collectively created an industrial edge that is broadly internet-reachable and inconsistently monitored.
What the Program Did
The shift from OSPF to MPLS routing in 2016–2017 was motivated by exactly this problem, acknowledged directly in the 2019 paper: expanding reliable IP transport for operational reasons had simultaneously expanded the attack surface. That was an honest engineering mistake, and documenting it is part of the value of the case study.
The architectural response was twofold. First, the MPLS routing fabric provided engineered traffic control that OSPF’s dynamic self-configuration cannot. Traffic paths were defined and managed, not discovered. Second, UTM firewall systems designed for ICS/SCADA environments were deployed not only at the network perimeter but at every internal segmentation boundary, including at each substation. The result was that even a device reachable from outside the network — a cellular gateway, a remote access appliance — could not move traffic laterally into the operations zone without traversing an explicit, allow-listed conduit.
Deep packet inspection was applied at zone boundaries for DNP3, Modbus, and SEL protocol traffic specifically. An adversary who compromised an edge device and attempted to use those protocols across a zone boundary would encounter a firewall that understood those protocols at the application layer, not just the port and address level.
| Lesson for OperatorsThe edge device is not the security boundary. Your architecture is. A compromised cellular gateway that cannot reach anything beyond an isolated conduit with allow-listed OT protocols has a bounded blast radius. The same device on a flat network is a door into everything. |
Gap 3: Legacy Systems and Safety Constraints
What the Dragos Report Describes
Many critical OT systems are old, fragile, and safety-critical. Operators cannot push agents, run aggressive scans, or patch legacy controllers without risking process instability. Patch cycles are often measured in years because changes require engineering validation and planned outages. This creates a persistent tail of unpatched, uninstrumented systems.
What the Program Did
The design philosophy throughout treated legacy as a given, not a problem to be solved. The documented design principle — assume legacy exists and design to contain it — produced a specific architectural response. Legacy RTUs, protection relays, and historians were placed inside protected sub-zones where their behavior was bounded by explicit conduit definitions. Broadcast and discovery protocols were terminated at zone boundaries. These devices were prevented from initiating traffic toward the operations zone or the enterprise network.
This is architectural containment, and it is the correct engineering answer to the legacy patching problem. You do not secure a DNP3 RTU running on a legacy embedded OS by patching it. You secure it by ensuring that its compromise cannot propagate — that the blast radius of any misbehavior or intrusion is bounded by the zone architecture to a consequence-manageable domain.
The approach also addresses the problem of intrusive scanning. You do not need to actively scan a legacy device that sits inside a zone with allow-listed, direction-specific conduits. The conduit policy itself defines what the device is permitted to do. Deviation from that policy is an observable event that requires no scanning.
| Lesson for OperatorsLegacy is a permanent condition of OT environments, not a temporary one. Design for it architecturally. A legacy device inside a well-defined zone with bounded conduits is a manageable risk. The same device on a flat network is unmanageable. |
Gap 4: Low-Noise “Living Off the Land” Tradecraft
What the Dragos Report Describes
Volt Typhoon and related threat groups are explicitly designed to be quiet, long-term pre-positioning operations. They use valid accounts, built-in administrative tools, and native protocols rather than custom malware, making them nearly indistinguishable from legitimate administrative activity. Even mature SOCs can miss these actors for years without OT-aware detection logic and behavioral baselining.
What the Program Did — and Did Not Do
This is the gap that requires the most careful characterization. The cooperative program laid the foundation for living-off-the-land detection, but it could not, at the resource level of a rural G&T cooperative in 2017–2019, deploy the specialized OT threat-hunting capability needed to reliably detect a sophisticated nation-state actor using valid credentials and native tools.
What the program did address was the underlying enabling condition: the absence of a behavioral baseline. An adversary who uses valid credentials and native protocols is invisible in an environment with no traffic baseline, no behavioral profile of legitimate administrative access, and no zone-to-zone monitoring. The centralized SIEM deployment, combined with per-zone firewall baseline monitoring, Active Directory user and device tracking, and 802.1X network access control, created the reference state against which anomalous administrative behavior becomes observable.
Multi-factor authentication for remote access and administrative functions, combined with 802.1X certificate-based device authentication, directly reduces the utility of stolen credentials. A valid username and password, without the second factor and without a valid 802.1X certificate on an authorized device, do not authenticate into the managed network. This significantly narrows the available living-off-the-land pathway.
The honest assessment is that containing this threat fully requires OT-specific threat intelligence, behavioral analytics tuned to OT protocol baselines, and 24/7 specialized threat hunting — capabilities that scale with resources in ways that other architectural controls do not. The cooperative program built the necessary foundation. The national problem requires investment at a different scale.
Gap 5: Scale, Fragmentation, and Uneven Maturity
What the Dragos Report Describes
U.S. critical infrastructure is fragmented across thousands of operators with very uneven security maturity. Some large utilities can experience OT-impacting incidents in a single day. Smaller water districts, cooperatives, and municipal utilities often lack staff, budget, and specialized OT security expertise — yet they operate internet-reachable equipment in the same threat space. Nation-state actors only need a subset of these environments to remain accessible to preserve pre-positioned access.
What the Program Did
This cooperative cluster was, in this period, exactly the kind of organization the Dragos report identifies as most at risk. It was a rural generation and transmission cooperative — actually a cluster of cooperatives — with the resource constraints typical of that class of operator. The documented program history includes explicit acknowledgment of mistakes: an initial focus that was too narrow on NERC CIP Low compliance without adequate attention to broader architecture, an underestimation of scope that required a major Phase 2 pivot, and staff resistance to security controls perceived as operational obstacles.
These are not the challenges of a large IOU with a dedicated security team. They are the challenges of a rural cooperative trying to do serious security work with limited resources. The design adaptations made under those constraints are precisely why this case study has practical value for the organizations identified by the Dragos report as most exposed.
The multi-vendor best-of-breed approach — selecting best-in-class tools for routing, firewalls, monitoring, and incident response rather than a single integrated vendor solution — was motivated in part by the need to avoid lock-in in an environment with limited budget flexibility. The dual-use monitoring strategy was motivated in part by the need to justify the monitoring investment on operational grounds. These adaptations for resource-constrained environments are replicable. They do not require an IOU-scale budget.
| Lesson for OperatorsConsequence-driven design scales down. You do not need a large organization to implement zone-and-conduit segmentation, MPLS traffic engineering, and dual-use monitoring. You need the right engineering questions and the discipline to make architectural decisions around consequence rather than convenience. |
Gap 6: Absence of Historical Telemetry
What the Dragos Report Describes
Many intrusions will never be identified because there is no historical telemetry to reconstruct what happened. Some compromises are limited to reconnaissance and credential theft with no operational anomaly to trigger an investigation. By the time defenders harden one set of gateways, actors have shifted to new footholds.
What the Program Did
The centralized SIEM and log aggregation deployment was the direct response to this problem. All firewall events, router SYSLOG output, SCADA server event logs, and Active Directory access logs were aggregated into a common collection system with retention policies that preserved historical records for retrospective analysis. The practical effect was that the organization created an audit trail, as the Dragos report identifies as absent in most OT environments.
The distinction between having logs and having useful logs is worth making explicitly. This program did not simply collect events. It established per-zone traffic baselines against which the logs were interpreted. A firewall event showing traffic from a legitimate management host to a SCADA server using DNP3 during normal operating hours is noise. The same traffic pattern at 0200 hours from a source address that has not appeared in the zone baseline for that communication is an investigable anomaly. The baseline is what makes the log useful.
V. Summary: Gap Coverage Matrix
The table below summarizes the degree to which the East Texas cooperative program addressed each structural gap identified in the 2026 Dragos report.
| Dragos 2026 Gap | Program Response (2019) | Coverage |
| Structural visibility gaps in OT | Centralized SIEM with per-zone baselines; dual-use NOC/SOC monitoring; asset discovery via instrumentation | Direct – Strong |
| Overexposed industrial edge and weak segmentation | MPLS traffic engineering; ICS/SCADA UTM firewalls at all boundaries; per-substation isolation zones; allow-listed conduits with DPI | Direct – Strong |
| Legacy systems and safety constraints | Architectural containment in protected sub-zones; broadcast termination at boundaries; no intrusive scanning required | Direct – Strong |
| Low-noise living-off-the-land tradecraft | MFA and 802.1X credential controls; behavioral baselining; Active Directory tracking. Full SOC hunting capability is not achievable at a cooperative scale | Partial – Foundation Built |
| Scale, fragmentation, and uneven maturity | Demonstrated consequence-driven design at rural co-op scale; dual-use monitoring; multi-vendor best-of-breed approach within resource constraints | Addressed by Example |
| Absence of historical telemetry | Centralized SIEM with log aggregation and retention; firewall, router, SCADA, and AD logs preserved for retrospective analysis | Direct – Strong |
VI. What This Means for Operators Today
The engineering work completed across the East Texas cooperative network from 2009 through 2019 was not designed in response to Volt Typhoon. That threat group was not publicly attributed until 2023, years after the program concluded. This work was designed in response to the engineering problem at hand: how to build and secure an OT and telemetry network spanning dozens of substations, multiple cooperatives, and nearly 900 MW of diverse generation assets, under real operational constraints, with the resources available to rural electric cooperatives, while maintaining 24/7/365 grid reliability and progressively addressing NERC CIP obligations as they came into force.
The fact that this engineering-first, consequence-driven approach directly addresses the structural conditions identified by the Dragos 2026 report is no coincidence. It is the outcome of starting from the right question. The right question in OT security is not what the compliance framework requires. It is not what specific threats are being countered. The right question is: what physical consequence could a cyber pathway cause, and how do we design the network so that the answer to that question is bounded, observable, and recoverable?
Every major decision in this program traces to that question. The MPLS migration, the zone-based segmentation to the substation level, the ICS/SCADA UTM firewall deployment, the dual-use monitoring architecture, the SIEM with behavioral baselines — all of it is the engineering answer to that question applied to a specific operational environment.
For operators evaluating their current posture against the Dragos findings, the practical takeaway is this: the solutions are not exotic. They were available in 2019. They are available today. The organizations that remain exposed are not exposed because the technology does not exist. They are exposed because the architectural decisions that create structural resistance to persistent adversary access have not been made.
Making those decisions requires accepting several operational realities:
- Legacy systems will not be replaced on a timeline that outpaces the threat. Design for containment, not elimination.
- Reliable IP connectivity for operational purposes and security exposure go hand in hand. Every remote access convenience added without architectural controls is a potential foothold.
- Monitoring without a baseline is noise. Zone-and-conduit segmentation creates the bounded observation domain from which a baseline becomes meaningful.
- The SIEM is only as useful as the retention and baseline policies behind it. Logging events you cannot interpret is not the same as having telemetry.
- Dual-use monitoring — treating security monitoring as a subset of operational monitoring — is the resource-constrained operator’s answer to the staffing problem. The same infrastructure that supports NOC operations can support SOC operations if the architecture is designed for it from the start.

VII. Conclusions
The Dragos 2026 OT Cybersecurity Report describes a national-scale problem that will not be fully resolved in the near term. The structural conditions enabling persistent adversary access are embedded in how OT networks were built and how they must be operated. Complete eradication is not achievable.
Containment, observability, and recoverable architecture are the achievable goals. The engineering logic needed to achieve them was documented in 2019 at a rural generation and transmission cooperative in East Texas. It is available to any operator willing to start with the right engineering question and make architectural decisions based on consequences rather than compliance or convenience.
The Dragos report is a useful and important contribution to the field. But the engineering response it implies is not new. For those of us who worked through these problems at the operational level — in rural cooperatives, with real equipment, under real operational constraints — the report’s findings look less like revelation and more like confirmation of what the work already told us.
The question for every OT operator reading this report is whether their current architecture gives them a fighting chance to detect lateral movement before it reaches the consequence-critical pathways, and to recover with confidence when it does. If the answer is uncertain, the path forward is to start with consequence mapping and build from there.
References
Dragos, Inc. (2026). OT Cybersecurity Report: Adversaries Increase Real-World Impact. Dragos Platform Intelligence.
Hargrove, J. E. (2019). Effective OT Cyber Security for Modern Grid Operations — One Cooperative’s Approach. Presented at 2019 IEEE Rural Electric Power Conference (REPC). IEEE.
Hargrove, J. E. (2009–2019). Grid IP Cyber Project Engineering Plans and Technical Documentation. Unpublished internal engineering documents, East Texas rural electric cooperatives (anonymized).
Hargrove, J. E. (2025). Cyber-Informed Grid Operations: Consequence-Driven Network Design for OT Security. JohnEHargrovePE Consulting. Reframed using INL Cyber-Informed Engineering.
Idaho National Laboratory. (2023). Cyber-Informed Engineering. U.S. Department of Energy.
NIST. (2024). Cybersecurity Framework 2.0. NIST CSWP 29. National Institute of Standards and Technology.
CISA. (2025). Cross-Sector Cybersecurity Performance Goals, Version 2.0. Cybersecurity and Infrastructure Security Agency.
Microsoft Threat Intelligence. (2023). Volt Typhoon Targets U.S. Critical Infrastructure with Living-off-the-Land Techniques. Microsoft Security Blog.
NERC. (2023). Critical Infrastructure Protection Standards (CIP-005 through CIP-009). North American Electric Reliability Corporation.
IEC. (2013). IEC 62443: Security of Industrial Automation and Control Systems. International Electrotechnical Commission.
Center for Internet Security. (2021). CIS Top 20 Critical Security Controls. CIS.
NRECA. (2018). Rural Cooperative Cybersecurity Capabilities (RC3) Program. National Rural Electric Cooperative Association.
John E. Hargrove, P.E. (TX) • JohnEHargrovePE Consulting • Buna, Texas
Four decades of experience in telecommunications, OT networks, and critical infrastructure cybersecurity.





